Between IoT botnet attacks, Bitcoin ransomware, and the weekly cadence of high-profile data breaches, doing anything on the internet feels like playing Russian Roulette.
And that’s just for normal people using it.
If you’re a developer, you’re partially responsible for protecting all those normal people from the horrors of whatever LulzSec are up to right now. The least you can do is make sure your website isn’t an accessory to their nefarious activities.
Thankfully, you do not have to brave the black hat darkness alone.
Mike Sherov made an egghead course that covers a whole series of web security essentials
I am (thankfully) not responsible enough for anyone to put me in charge of security for an important website. But I was still curious.
I wanted to know what the current landscape of internet risk looks like. How, exactly, is LulzSec going to hack into my mainframe in 2020?
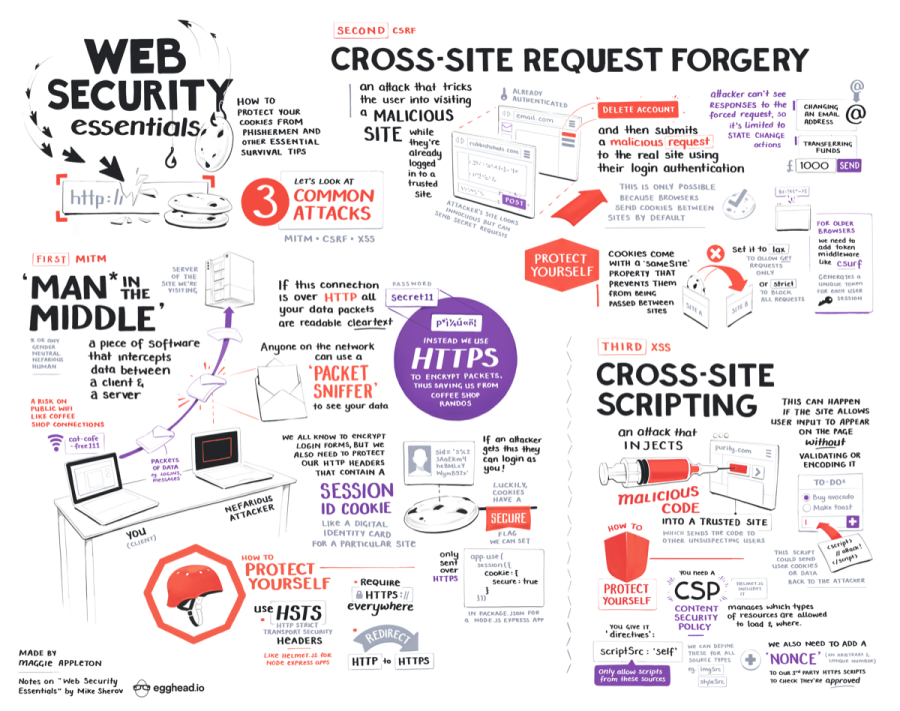
Here’s my illustrated notes from Mike’s course that should give you a big picture overview of what to should look out for.

Turns out there’s a small set of fairly well-known and easy to defend attacks that we can protect ourselves from:
- Man in the Middle (MITM)
- Cross-Site Request Forgery (CSRF)
- Cross-Site Scripting (XSS)
Shielding yourself from these three is a great starting point. It’s at least enough to keep the script kiddies out.



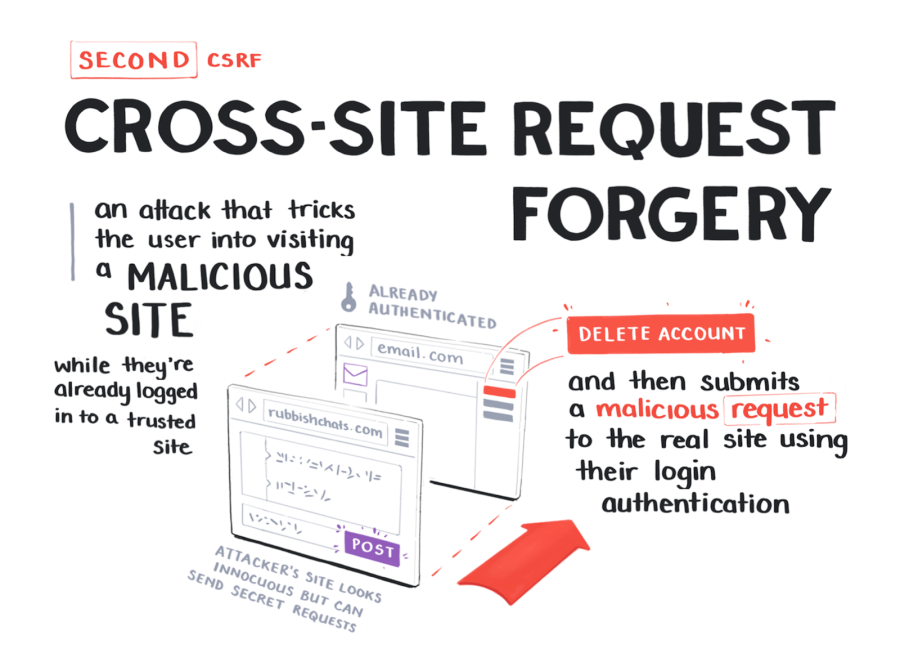

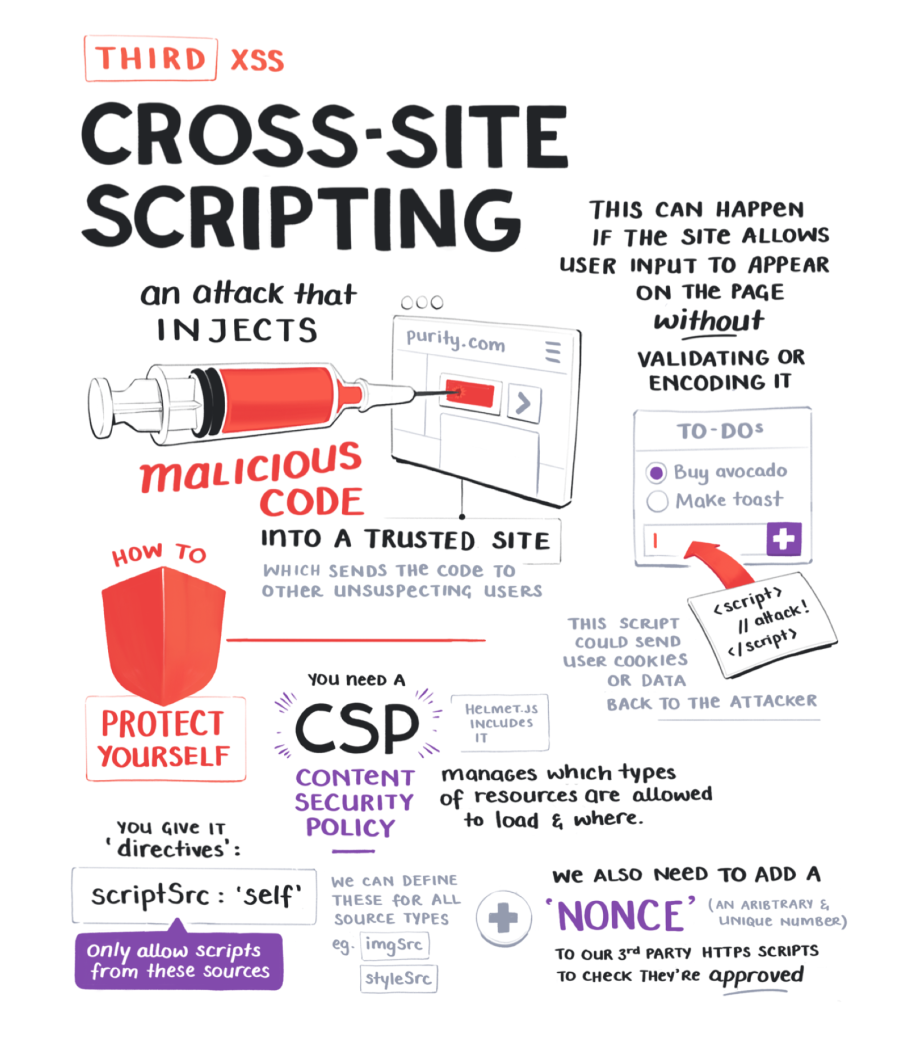
Keeping out this trio of attacks will go a long way.
If (unlike me) you are responsible enough to be in charge of security for a moderately-sized website, it might be worth double checking you have these protections in place.
Better safe than sorry. Especially when sorry means you end up on the front page of Hacker News in this week’s edition of obviously preventable security breaches.
Want more illustrated notes on web development?
Take a look at Testing Apps with Cypress Testing Apps with Cypress
Illustrated notes on how to test web apps with Cypress , The JAMStack, Gatsby & Contentful The JAMStack, Gatsby & Contentful
Illustrated notes on the JAMstack, Gatsby & Contentful or A Fresh Serving of JavaScript ES2019 A Fresh Serving of JavaScript ES2019
Illustrated notes on the new language changes in JavaScript ES2019